I saw Phil Collins in concert back in 2005. There was one set of drums out on the stage, he walks out, holds up some sticks, and started to really get down on the drums. After around five minutes another set of drums comes up from the stage with a second drummer. Five minutes of two drummers. Then a third drummer, five more minutes of three drummers. Fifteen minutes of nothing but drums going wild. Awesome.
Here is another version of Phil Collins signature song. Heading to Nacogdoches for the weekend. Hope you have a great one also and enjoy the music.
Police Work, Politics and World Affairs, Football and the ongoing search for great Scotch Whiskey!
Friday, March 31, 2017
This is how a cop thinks when he has overtime! :<)
I worked 17 hours of glorious overtime during the Super Bowl (and 13 hours the day before) and it ended in the greatest check of my career. I can related to this officer.

The bad thing was as I was dreaming about that great check, I knew it was already spent! :)

The bad thing was as I was dreaming about that great check, I knew it was already spent! :)
Labels:
Police
Thursday, March 30, 2017
Latest example of the Ferguson Effect. The Windy City is blowing now...
Thanks in large part to the War on Cops, led by the Eric Holder "Just-Us" Department, cops thought out the nation are pulling back from assertive police actions. As before cops would go out, stop people who are conducting suspicious activity (e.g. making actions that show selling narcotics in an area know for narcotics sales) and finding on them weapons, drugs, or warrants. Well thanks to B Hussein Obama and his community activists, the police in Chicago are not going to go out and be forceful. They will hold back, run their calls for service and not get in trouble. If that means the turd who would have been stopped with a pistol in his pocket, booked for felon in possession of a firearm, stopping him from going to commit a murder, well....B Hussein Obama and his friends will have made their point.
From the Windy City...
Run those numbers. Assume 650,000 per year, you've dropped to around 110,000 per year now. One fifth of the previous numbers. Well how has that worked out:
Murders 2013: 422
Murders 2014: 428
Murders 2015: 495
Murders 2016: 747
Murders 2017: 134 (As of March 28, 2017)
Do you notice something. The "...agreement the city reached with the ACLU in 2015..." and next year murders once by 25%. Really working well there American Criminal Lovers Union. Sucks if you live on the South Side.
Well, you got something changed alright. in three years, you got 300 more murders a year. Well done Karen, well done.
I am terrified to think what else would you want done. Ain't increasing the homicide rate 50% in three years enough?
Suggestion. Maybe if the CPD brought the homicide rate down it would help their "public trust." You know, do "cop work."
Lady, you are so brain vacuumed it's painful to think you made it out of high school, much less law school. Get this Karen, it's not the weapons, it's the people. I don't need a gun to murder you or injury you. But I'm stopped, arrested for the crack in my shoe and put away for a few days, I wasn't able to go down the street, see another thug with different bandanas on his jeans and have my homies shank him. Again, if I'm not on the street, I'm not committing more crime. See how that works out.
This is in no way the fault of the front line men and women of CPD. They've been targeted by the Holder/Lynch "Just-Us" Department and the B Hussein Obama regime. And the Emanuel administration has left you out to dry, so I understand why you're holding back. Hopefully we get this "agreement" lifted soon and you can start policing again. God help the city of Chicago.
From the Windy City...
Study: Chicago stop-and-frisk numbers drop, more work needed
The study revealed a dramatic decrease in the number of stops since an ACLU of Illinois lawsuit, but found that officers were still targeting racial minorities
By Don Babwin and Sophia Tareen Associated Press
CHICAGO — A study of the Chicago Police Department's stop-and-frisk procedures released Friday revealed a dramatic decrease in the number of stops since an American Civil Liberties Union of Illinois lawsuit, but found that officers were still targeting racial minorities.
The report by former U.S. Magistrate Judge Arlander Keys, the first one issued under an agreement the city reached with the ACLU in 2015, was not surprising to ACLU officials. The organization expected the decrease because of changes in the law and a deal the organization reached with the department that requires officers to fill out more detailed reports of stops than they once did.
According to the report, the number of investigatory stops fell from more than 1.3 million in 2014 and 2015 to just over 54,000 in the first six months of 2016...
Run those numbers. Assume 650,000 per year, you've dropped to around 110,000 per year now. One fifth of the previous numbers. Well how has that worked out:
Murders 2013: 422
Murders 2014: 428
Murders 2015: 495
Murders 2016: 747
Murders 2017: 134 (As of March 28, 2017)
Do you notice something. The "...agreement the city reached with the ACLU in 2015..." and next year murders once by 25%. Really working well there American Criminal Lovers Union. Sucks if you live on the South Side.
"...We needed something to change, those numbers just could not continue," said Karen Sheley, director of Police Practices Project at the ACLU of Illinois. She said the rate of stops in Chicago on a per capita basis was more than four times than it was in New York. The number of stops has dropped dramatically in New York as well...
Well, you got something changed alright. in three years, you got 300 more murders a year. Well done Karen, well done.
...Chicago police spokesman Anthony Guglielmi said the department would "carefully review the recommendations" and work on implementing reforms while "protecting civil rights of the public." And Chicago's city attorney, Edward Siskel, said the report documents the city's "dedication to fully adopting the new policies and procedures."Mr. Guglielmi, I've reviewed the recommendations and they suck. Mr. Siskel, are you looking at the murder rate in your city? Perhaps you should check that.
But Sheley said more work needs to be done, pointing out that while the number of stops has dropped, blacks still make up more than 70 percent of those who are stopped even though they account for about a third of Chicago's population...
I am terrified to think what else would you want done. Ain't increasing the homicide rate 50% in three years enough?
The new report comes as Chicago police are trying to regain public trust in the wake of a video that shows a white officer fatally shooting black teenager Laquan McDonald in 2014. An ensuing Justice Department report this year found the Police Department had a long history of civil rights violations and excessive force.
Suggestion. Maybe if the CPD brought the homicide rate down it would help their "public trust." You know, do "cop work."
The report also included a statistic that might surprise those who criticized the department, both on and off the force, when the 2015 agreement with the ACLU was reached. At the time, critics wondered if reducing the number of stops might decrease the number of illegal guns taken off the street. But the report found that of the 18,364 stops involving a pat-down search, frequently called stop-and-frisk, 465 weapons were recovered — a fraction of the thousands of guns the department takes off the street every year...
Lady, you are so brain vacuumed it's painful to think you made it out of high school, much less law school. Get this Karen, it's not the weapons, it's the people. I don't need a gun to murder you or injury you. But I'm stopped, arrested for the crack in my shoe and put away for a few days, I wasn't able to go down the street, see another thug with different bandanas on his jeans and have my homies shank him. Again, if I'm not on the street, I'm not committing more crime. See how that works out.
This is in no way the fault of the front line men and women of CPD. They've been targeted by the Holder/Lynch "Just-Us" Department and the B Hussein Obama regime. And the Emanuel administration has left you out to dry, so I understand why you're holding back. Hopefully we get this "agreement" lifted soon and you can start policing again. God help the city of Chicago.
STRATFOR: Russia's New Wave of Protests, March 28, 2017
Russia's New Wave of Protests
Russia's New Wave of Protests is republished with permission of Stratfor.
Russia's New Wave of Protests is republished with permission of Stratfor.
Labels:
Russia
A new version of a classic...
For kids of the 60s and 70s, Loony Tones cartoons were awesome. Now someone has made a new cartoon, with modern technology. Enjoy.
Wednesday, March 29, 2017
Trump, the doer
Long time friend, fellow retired Army officer, and occasional writer Mike Ford has another great piece in the American Thinker. Enjoy.
Trump, the doer
The Democrats have once again rolled the Republicans. They did it, as always, by controlling the terms of the discussion.
All throughout the Obama era, Republicans (quite rightly) complained about Obamacare. They passed a seemingly unending series of repeal bills, some of which made it through the Senate and one of which actually made it to President Obama's desk...for an ultimate veto.
How did the Democrats win this time? By constantly harping on the Republican Party: So what's your plan, Republicans? The Republicans, true to form, backed down and bought into the Democrat/Statist narrative of the necessity for federal involvement intervention in medicine and promised a replacement plan. Their campaign slogan changed from Repeal! to Repeal and Replace. Thus, no matter what, the least that would happen is that medical care in the United States would remain to the left of where it was in 2008, giving the Statists the win. Prime Minister Margaret Thatcher once referred to this as the "ratchet effect."
Speaker Ryan owns a large chunk of this, along with his long serving establishment posse. However, President Trump also has some ownership, and here is why. Donald J. Trump has two major attributes. On the upside, he is a doer. He knows and has demonstrated that he can get things done...on time and under budget. Not only was he a success in the business community, but as a political novice, he beat the well funded Clinton machine...a machine that spent almost twice what he did and employed over six times as many paid operatives. Any way you look at it, President Trump is a guy who gets stuff done, does it in a cost-effective way, and does so with his very own form of panache.
On the downside, there is Trump's attribute: he's a doer. When confronted with a problem, his first instinct is to jump right in and begin to solve it. And, as I mentioned above, he is usually, or should I say unusually, successful. However, as president of our constitutional republic, this might not always be the best method, as recently demonstrated by his active support of the failed Ryan plan to "repeal and replace" Obamacare. Ryan's plan, often referred to as "Obamacare Lite," failed to garner enough votes, forcing him to pull it from consideration on the floor of the House.
In his remarks after Speaker Ryan pulled the bill, President Trump spoke of the future, saying, "But I want to have a great health care bill and plan, and we will. It will happen. And it won't be in the very distant future."
Although Trump's remarks and earlier actions were those of a doer, conservatives have issue with this philosophy when applied to federal legislation in general and health care specifically. It's a big reason why Ryan's plan failed to garner support from the House Freedom Caucus. Conservatives don't want a (Trump's words in italics) "Big beautiful (federal) health care plan." Such a plan would, by necessity, be run from D.C., continuing the growth of the federal government and its pervasive influence in our daily lives. Conservatives want full repeal of Obamacare – and, after that, a series of standalone bills that remove the federal government from health care decision-making and funding, constraining it to its constitutional functions while allowing the free market to regulate innovation, quality, and costs.
In the future, Trump, the doer, might consider asking one question before jumping in to fix a problem, whether it be health care or anything else. The first thing he should ask is, "What part of this problem, if any, is a federal (per the U.S. Constitution) issue?" Had he done this with Obamacare, he might have found that the "federal issue" with Obamacare and the rest of health care environment in the United States is that the federal government is way too involved in the first place. Instead of a federal plan that does things, the plan might have been simply for the federal government to stop doing some things.
Mike Ford is a sometime contributor to American Thinker who has learned over multiple decades that the first step in the Problem Solving Process is to Identify the Problem. As Ronaldus Magnus opined, "Government is the problem."
Nuclear blast from 1953
From Popular Science, the video of a 1953 nuclear test. It shows shows how the house is "slowly" destroyed over a fraction of a second.
Watch a 1953 nuclear blast test disintegrate a house in high resolution | Popular ScienceThanks Mike K for the link.
Labels:
History
Saturday, March 25, 2017
What a week…
Just spoke with one of my fellow sergeants who was recovering from Thursday/Friday like me.
Wednesday, it started. The board of calls was just overloaded. I hate to leave Night Watch with so much, but we had to. Another agency asked for assistance with a non-emergency call. My dispatched asked about it and the only answer I could give her was, “When I got someone, I’ll send them.”
Thursday was actually pleasant. Things were going steady and I was thinking I would get off on time. I’m guessing someone said, “It’s really quiet tonight…”
At 915pm one of my units had a runner and fortunately the other sergeant went to handle the supervisor duties. Well five minutes after that I hear, “We need more units!,” and I drove off the help. We had two teenage siblings fighting themselves initially, then fighting the cops. We were just getting them under control when the family that called us is about to attack everyone.
We get our suspects moved off and we had just gotten the matter handled (charges accepted, booking blotters filled out, etc) when we hear, “Shots fired! Need back up now!” Needless to say we’re all heading over there. Fortunately the cops were fine.
After a ton of paperwork, I get home at just past 400am, let my uniform drop the to the floor and I don’t remember falling asleep. And waking up after 900am and not being able to go back to sleep. And I have more paperwork to complete so I need to be in at noon. Coffee, quick shower, fresh uniform, drive in, stop by Starbucks for a large Mocha Frap with a shot of espresso (caffeine…the all natural substitute for sleep!), pick up some fried fish from the local Catholic church (if I’m going to hell it’s not for eating meat on Friday during Lent!) and I get a jump on the paperwork. I looked at a couple of other sergeants who were not there on Thursday and said, “You picked a great day to take off!” And on a Friday, thank you God, managed to get off on time!
I get home and I’m too tired to sleep. I just get some whiskey and read a bit until I finally die off. SEVEN HOURS OF SLEEP, thank God!
My fellow sergeant had worked 24 straight on a couple of hours of sleep. Spoke to him this morning and he had also experienced the “sleep of the dead” and was sounding a lot better. I just didn’t believe all the energy I had after a good night’s rest.
To the cops out there, for all the burdens of this job (the strange hours, the missed family/friends) there is something about it. The Watch is a calling, something most can’t do. And thankfully, there are men and women to do it!
Be safe out there!
Wednesday, it started. The board of calls was just overloaded. I hate to leave Night Watch with so much, but we had to. Another agency asked for assistance with a non-emergency call. My dispatched asked about it and the only answer I could give her was, “When I got someone, I’ll send them.”
Thursday was actually pleasant. Things were going steady and I was thinking I would get off on time. I’m guessing someone said, “It’s really quiet tonight…”
At 915pm one of my units had a runner and fortunately the other sergeant went to handle the supervisor duties. Well five minutes after that I hear, “We need more units!,” and I drove off the help. We had two teenage siblings fighting themselves initially, then fighting the cops. We were just getting them under control when the family that called us is about to attack everyone.
We get our suspects moved off and we had just gotten the matter handled (charges accepted, booking blotters filled out, etc) when we hear, “Shots fired! Need back up now!” Needless to say we’re all heading over there. Fortunately the cops were fine.
After a ton of paperwork, I get home at just past 400am, let my uniform drop the to the floor and I don’t remember falling asleep. And waking up after 900am and not being able to go back to sleep. And I have more paperwork to complete so I need to be in at noon. Coffee, quick shower, fresh uniform, drive in, stop by Starbucks for a large Mocha Frap with a shot of espresso (caffeine…the all natural substitute for sleep!), pick up some fried fish from the local Catholic church (if I’m going to hell it’s not for eating meat on Friday during Lent!) and I get a jump on the paperwork. I looked at a couple of other sergeants who were not there on Thursday and said, “You picked a great day to take off!” And on a Friday, thank you God, managed to get off on time!
I get home and I’m too tired to sleep. I just get some whiskey and read a bit until I finally die off. SEVEN HOURS OF SLEEP, thank God!
My fellow sergeant had worked 24 straight on a couple of hours of sleep. Spoke to him this morning and he had also experienced the “sleep of the dead” and was sounding a lot better. I just didn’t believe all the energy I had after a good night’s rest.
To the cops out there, for all the burdens of this job (the strange hours, the missed family/friends) there is something about it. The Watch is a calling, something most can’t do. And thankfully, there are men and women to do it!
Be safe out there!
Tuesday, March 21, 2017
Use of force. On a woman.
I recall trying to take a man in a wheelchair into custody. My partner and I were at it for almost five minutes and damned I was exhausted.
Notice this officer is much larger than the woman he is trying to take into custody and it still takes over 4 minutes and the assistance of another officer to get her under control. And the driver could have gotten into the fight, where it might have elevated from there.
Good work on this and I'm glad you're ok:
Notice this officer is much larger than the woman he is trying to take into custody and it still takes over 4 minutes and the assistance of another officer to get her under control. And the driver could have gotten into the fight, where it might have elevated from there.
Good work on this and I'm glad you're ok:
Saturday, March 18, 2017
Some people just don't get it....
One of the questions I have when I pull someone over is, "Do they get a ticket or warning." With people like this, the question answered itself.
Friday, March 17, 2017
Ouch.....
I've had my feet run over twice and it's no fun. In this short video a Saudi prince seems to not like getting a ticket and tries to drive off. Mistake.
Tuesday, March 14, 2017
The threat of cyber attack to our energy industry.....
Last year I finished my master's degree (Again, thank you God that's over!) in Intelligence Studies, with a focus in Homeland Security. I got interested in the threat of cyber warfare to our critical infrastructure. One of the books I read was Countdown to Zero Day: Stuxnet and the Launch of the World's First Digital Weapon, documenting the development and deployment of the Student virus against the Iranian nuclear program. It also reviewed how control of large infrastructure systems (power generation, dam control, etc) started to be automated in the 1970s. But back then there was no Internet and few software companies, so the operating systems were proprietary. In the 1990s we started to standardize them to a Windows or Lynux system, which made them more functionals, but also gave adversaries a "in" to the system.
In 2007, the Department of Energy wanted to test this threat. They purchased an old 30mw generator and paid a contractor to build a virus to destroy it. The contractor put thirty lines of code into the operating system and within three minutes this generator was a pile of scrap metal. He blocked the liberation system while having the motor go at full speed, all the while having the monitoring stations reading normal reading. A sobering sight.
From the Sunday Houston Chronicle, a good article on the threat of the this type of attack on a critic asset.
In 2007, the Department of Energy wanted to test this threat. They purchased an old 30mw generator and paid a contractor to build a virus to destroy it. The contractor put thirty lines of code into the operating system and within three minutes this generator was a pile of scrap metal. He blocked the liberation system while having the motor go at full speed, all the while having the monitoring stations reading normal reading. A sobering sight.
From the Sunday Houston Chronicle, a good article on the threat of the this type of attack on a critic asset.
Hackers prove oil networks are vulnerable to attack
By Collin Eaton
Refineries, such as this one along Texas 225 in Deer Park, can be vulnerable to
cyberattacks, even with fencing, high-tech sensors and security teams.
The computer hacker crouched low in thick brush on a cold December night, just beyond the fence line of his target — a massive U.S. oil refinery.
Wearing night-vision goggles and dressed in black, he swung a rubber mallet into the dirt, trying to produce vibrations to distract the plant’s ground-penetrating radar system. He swung again and again. Flashlights emerged from adistant building, then disappeared.
Soon a train roared by, providing the cover his team needed. Quickly, two more men appeared from the shadows. They threw a wool blanket over a 16-foot barbed wire fence, climbed over and rushed to a small building housing the facility’s vital computer controls.
The door had an electronic lock, a badge reader and a plate to thwart lock picking. But the intruders caught a break. The door didn’t sit properly in its frame, leaving just enough space to shimmy it open.
Within moments, they had planted a small device, about the size of a credit card, designed to begin penetrating the refinery’s controls systems.
“Bingo!” crackled from the radio inside a white SUV adorned with a phony logo of the refining company, some 200 yards away. From there, Jeremiah Talamantes gave the signal to leave — “Rabbit!”
As the other hackers hopped in the van, the driver’s nerves calmed. Then a stark reality set in.
“We’ve used a couple hundred dollars in gear, and we were able to break into a refinery without anyone knowing,” said Talamantes, president and managing partner of RedTeam Security in Minnesota. “The implication is pretty devastating.”
Talamantes was hired by the refinery to test its defenses against cyberattacks, and, like so many others, the mission was way too easy. Despite the refinery’s remote location, fencing, high-tech sensors and security team, his team was able to infiltrate its network and potentially wreak havoc.
In recent years, a growing cottage industry of boutique security companies has emerged as oil and gas companies seek outside help to protect their networks. In test after test, private specialists reveal what federal authorities say is a growing national security threat —control systems for valves, pumps, pipelines and refineries are among the most vulnerable targets to cyberattacks.
Often, security firms find that drillers, refiners and pipeline operators run facilities with outdated software and aging automated devices without built-in security. Some companies lack internal detection systems that would allow them to spot cyber intruders.
“We almost always get in,” said Jason Larsen, who leads a team at security firm IOActive that has operations in more than 30 countries. “Most of the time we’re not detected.”
Many energy companies are turning to security specialists to determine whether protocols and defensive software can withstand the creativity and determination of global hackers, said Larry Dannemiller, a cyber insurance broker for major U.S. insurance firms.
“Are all the dollars they’re spending actually making them more secure?” he said. “You have to test it.”
Talamantes shared a detailed account of his firm’s efforts to penetrate the refinery, located in the southeastern United States, so long as the company’s name wasn’t published. Executives were stunned by the intrusion, he said, believing a successful break-in would have taken a much larger team with more time, resources and expensive gear.
“We proved them wrong,” Talamantes said bluntly.
Global problem
From the mines of Chile to offshore platforms in the Indian Ocean to refineries in the United States, Jim Guinn has hacked just about every kind of energy facility.
“There’s not a refinery, power generation facility, oil terminal or platform that doesn’t have technology on it that we haven’t been able to infiltrate,” said Guinn, global cybersecurity leader for energy at Accenture Security consulting in Houston.
This grim assessment comes in spite of the industry’s hard-won progress in cybersecurity over the past few years. Before 2010, energy executives largely ignored the threat such attacks posed to their operations, said Gary Leibowitz, a board member of the Houston chapter of InfraGard, a group that works on cybersecurity issues with the FBI and private companies.
That year, the Stuxnet virus damaged thousands of centrifuges within Iranian nuclear facilities, demonstrating how computer viruses could be so destructive in the real world. Since then, many oil companies have made progress in hardening firewalls, bolstering anti-virus software and other defenses and improving cybersecurity practices.
“Companies are spending time and money on cybersecurity, and it’s across the board,” Leibowitz said.
Exxon Mobil, for example, bans its employees from using personal email and USB flash drives that can carry computer viruses and regularly sends simulated phishing emails to test whether workers will click on alluring links or open attachments, executives said at industry conferences. The company, like many other oil and gas companies contacted for this story, declined comment.
The oil and gas industry, however, remains at a disadvantage against sophisticated hackers, cybersecurity specialists said. The sheer size of the industry alone makes it difficult to secure thousands of devices in vast networks of pipelines, refineries and other facilities stretching across the continent.
In contrast, hackers have to look for only a small number of security flaws to exploit these systems, said Philip Quade, who recently retired as chief of the National Security Agency’s cyber task force.
“Just about anything,” he said, “can be penetrated by someone sophisticated and determined.”
Open to the public
In many cases, the resourceful hacker doesn’t need to develop new malware to get access to industrial controls — asimple internet search can do the trick.
A few years ago, Eireann Leverett, a cybersecurity researcher in the United Kingdom, used a public search engine to find more than 7,500 industrial devices that were linked to the internet. Fewer than 1 in 5 required any kind of authentication, such as passwords, to get inside.
Among the devices hackers have attacked through the internet are the lightweight sensors that run along thousands of miles of pipeline across the nation.
“We should be worried,” Leverett said.
Compromising a sensor on a pipeline could allow a hacker to alter readings of how much oil and gas is running through the pipeline, which could cause the systems to begin pumping more hydrocarbons, said Alvaro Cardenas, an assistant professor and cybersecurity expert at the University of Texas at Dallas.
“It might cause a pressure blast,” Cardenas said.
A few years ago, hackers succeeded in hijacking the modems attached to remote sensors owned by two North American pipeline and utilities companies, after finding them on a public search engine, said Guinn, one of the cybersecurity consultants that investigated the incident.
A power outage had caused the sensors to reset — effectively, turn off — their security settings, leaving them vulnerable to attack from the internet. In this case, the hackers used these devices to launch cyberattacks against other groups. If they had more nefarious ends, they could have crippled the pipelines, Guinn said.
“It’s possible to demonstrate catastrophic disruption in energy company assets,” he said. “We know it can be done.”
Wireless woes
Beyond the internet, industrial controls, sensors and other devices with wireless capabilities or radio transmitters are open to attack by hackers using long-range antennas.
In fact, an off-the-shelf drone attached with a wireless receiver could fly within range of a facility and intercept its wireless signals, according to cybersecurity specialists.
Jeff Melrose, principal security manager at industrial control vendor Yokagowa, piloted three white drones simultaneously over a parking lot in Stafford, demonstrating their maneuverability and potential for extending a hacker’s reach to capture wireless signals.
“Drones are coming into their own, and the things people can do with them will only increase,” said Melrose, noting that energy companies have reported drones buzzing by facilities or crashed with dead batteries nearby.
Security personnel at energy companies are more used to dealing with activists handcuffing themselves to valves, Melrose added. They rarely look up to see the threat from above.
“The question is,” he said, “are you thinking about the deviousness of your adversary?”
The Department of Homeland Security said network scanning and probing accounted for 79 cyber incidents involving industrial controls in 2014 and 2015, but it would not disclose additional details, citing security concerns.
Many companies have adopted advanced encryptions. Still, the most common security setting for wireless networks in energy and other industrial facilities remains the password-protected WPA-2 protocol, used for household wireless networks.
Skilled hackers could break into them in about two hours, said Kevin Dunn, senior vice president at the Austin offices of NCC Group, a security firm based in the United Kingdom.
“If this were a targeted attack,” Dunn said, “whether it be ‘hactivism’ or a nation-state, all they need is time and money and opportunity.”
Employee mishaps
Simple mistakes by workers can lead to devastating consequences.
Two years ago, Steve Mustard, a cybersecurity specialist for the nonprofit group Automation Federation, was delivering a lecture at a Western oil company’s office in Tunisia when the event came to an abrupt halt. The company’s anti-virus program had detected the destructive Stuxnet virus.
IT workers rushed to phones and computers, discovering an employee had accidentally uploaded the virus by plugging an infected thumb drive into his computer. They quickly tracked down and contained the virus.
Had the employee plugged that drive into a computer at a nearby oil production facility, chances are the company would never have caught the virus. It had no detection systems in place for the computer network controlling operations, Mustard said.
“Spills, potential worker injuries, explosions, fires — all of those things could happen,” Mustard said. “What you’ve got are very vulnerable systems that aren’t managed very well, and on the other side, an exponentially increasing number of threats.”
Physical threats
As Talamantes’ refinery caper shows, hackers don’t have to limit themselves to the internet to break into computer networks.
With long-range cameras, they can spend days watching workers entering front doors, so they can mimic their behavior and exploit weak spots to get inside, Talamantes said.
Before Talamantes and his team raided the oil refinery in December, they staked out the company’s corporate offices. They watched employees at nearby coffee shops and restaurants, managing to steal and clone badges.
Talamantes said he tries to stay within the bounds of what real hackers can do with a modest investment. In the refinery raid, his team carried only a small amount of gear, including a laptop, lock-pick set and a $35 device to tap the computer systems, all available on Amazon.
They used two 16-foot ladders, which they returned to Home Depot for a full refund, a set of four two-way radios and lock picks. Over the course of his career, Talamantes said, such tests have found plenty of security weaknesses, cyber and otherwise, that should worry the energy industry.
But the scariest part, he said, is that so much of hacking is low-tech, requiring little expertise.
“Anyone can do these types of things.”
Monday, March 13, 2017
STRATFOR: Russia's Evolving Borderlands, February 28, 2017
Stratfor Vice President of Global Analysis Reva Goujon and Senior Eurasia Analyst Eugene Chausovsky discuss the shifting political dynamics in Russia's periphery.
"Russia's Evolving Borderlands is republished with permission of Stratfor."
More detailed analysis on this issue can be found here:
In Europe's Borderlands, the Winds of Change Blow in Every Direction
February 28, 2017 | 08:00 GMT
By Eugene Chausovsky
Europe's borderlands are in flux. From the shores of the Baltic to the Black seas, and from the peaks of the Carpathians to the Caucasus mountains, each country in the borderlands between Europe and Russia is re-evaluating its foreign policy position in response to major geopolitical changes.
On the west of this group, the European Union is roiled by divisions in the wake of the Brexit vote and intensifying nationalist sentiments, as crucial elections take shape this year in France, Germany and possibly Italy. On the east, Russia has the ear of the new U.S. administration, which is seeking to improve ties with Moscow as it focuses more on the homefront. Though a major reconciliation is a stretch, even the possibility of an understanding or realignment with the United States has enabled Russia to grow more assertive in its periphery...
STRATFOR: The Marketplace in Space, November 18, 2016
I've been meaning to post this for the last few months. It's amazing what imagery is available now. In years past, getting a few pictures of large formations of troops or ships was a major effort. Now we apps for it. God knows we could not mount another Operation Overlord again. An interesting look at how satellite imagey has moved from the domain of governments to the commodity of the free market.
A satellite image shows an oil field burning near Iraq's Qayyarah
air base on Sept. 4. (DigitalGloba/AllSource Analysis)
Forecast
Though commercial satellite imagery is now available to every corner of the economy, the industry will largely stay focused on its original customers: government intelligence agencies.
Thanks to a number of novel concepts and technologies, imagery collection satellites will continue to evolve and proliferate at a faster and faster pace.
As companies try to keep up with the ever-expanding volume of imagery available, they will have to find better ways to store, analyze and manage it.
Analysis
DigitalGlobe, one of the largest commercial providers of satellite imagery, launched its WorldView-4 satellite into orbit last week, adding to the growing constellation of satellites circling the Earth. Thanks to these satellites, we have gotten accustomed to having vast amounts of imagery at our fingertips. From online mapping services like Google Maps to browsable databases like Microsoft's TerraServer, the widespread availability of aerial photographs has become the new norm.
But commercial satellite imagery was never intended to serve media outlets or households alone. Instead, the industry was largely built with one set of customers in mind: government intelligence agencies. Even now, the imagery that frequently makes its way to consumers in the private sector is still gathered with an eye toward intelligence requirements. In all likelihood this emphasis will not change much in the coming years, even as states' own collection capabilities continue to improve....
...Complete and Detailed Coverage
Since 1960, when the United States took its first photograph from space, nearly a dozen other countries have launched their own reconnaissance satellites. Over time, the capabilities of those satellites have evolved. At first, early models such as the Corona KH-1 took images with an equivalent resolution of 12 meters (39 feet). (In other words, the surface represented by a single pixel measured about 12 meters by 12 meters.) At this resolution, analysts could make out only large infrastructure, such as runways. But after a series of rapid innovations, satellites were able to take pictures at an equivalent resolution of 1.5 meters. By 1967, analysts could detect individual aircraft, ships and buildings from the images satellites produced. Of course, they still paled in comparison to today's photographs, whose 30-centimeter resolution allows analysts to identify specific weapons systems or even locate human silhouettes.
Modern satellites can deliver images more quickly now, too. The satellites belonging to the United States' initial Corona program carried film cassettes that were then dropped and recovered as they fell toward the Earth. Unsurprisingly, this method led to substantial delays in the photographs' arrival on the desks of analysts and policymakers. It wasn't until 1976, when Washington launched the first KH-11 Kennan spy satellite, equipped with a digital sensor, that images could be immediately transmitted to bases on the ground. Now the United States has 15 of these satellites — which are believed to be able to achieve resolutions as high as 15 centimeters — in orbit. Though much of Washington's satellite program since the KH-11's development remains classified, many believe the newer KH-13 series is operational as well. Regardless, the spread of cutting-edge satellites in space has dramatically increased the ability of the world's great powers to observe one another's actions — a change some have even credited with stabilizing the world by making it more difficult for countries to hide wrongdoing or secretly amass military power.
In Search of New Markets
Governments have not been the only ones pursuing better satellite abilities, either. In 1993, the first private satellite imagery company — WorldView Inc., which later became DigitalGlobe — burst onto the scene when it secured a U.S. license to sell its photographs. Since then, the market has grown exponentially as other giants such as Airbus and myriad smaller competitors followed in DigitalGlobe's footsteps. Thanks in part to increasing internet access and bandwidth worldwide, the industry has taken off, reaching corporations and publishing companies around the globe.
Nevertheless, the bulk of commercial satellite firms still receive most of their revenue from governments. The burgeoning businesses have given countries that are unable or unwilling to field their own satellites access to imagery they otherwise would not have had. Selling photographs to multiple clients has also made imagery far more affordable for consumers, and prices on most products are still falling. The cost of sending satellites into space is dropping quickly as well, reducing the amount of upfront investment required to develop private satellite fleets.
Plunging costs and rising demand have encouraged the sector to seek out new customers. Nongovernmental organizations have been of particular interest to commercial satellite companies, though beyond a small segment that cover conflict zones, nuclear proliferation and humanitarian crises, they have proved a difficult market to break into. The industry has had more success selling its goods to media outlets, but even then it faces tight restrictions on the sale of photographs that contain information on certain government activities, including the movement of troops....
Sunday, March 12, 2017
Arteries getting cleaner....
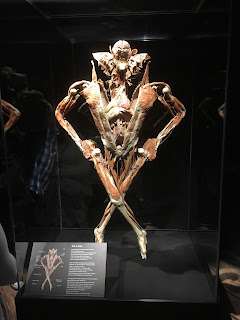
I spend a few hours this afternoon with my wife and 17 year old at the Bodyworlds exhibit at the Houston Health Museum. If you haven't seen it, do yourself a favor and spend some time there if you can. Even for a non-medical nerd like me it is fascinating, seeing the parts of the human anatomy and how they interact. Here is the "Split Lady" exhibit:
I was just surfing Facebook and I found this interesting took being worked on for treating blocked arteries. It is nothing short of incredibly in how we can treat ailments these days. Take a look at this. It's still in development, but damn, it look promising.
I was just surfing Facebook and I found this interesting took being worked on for treating blocked arteries. It is nothing short of incredibly in how we can treat ailments these days. Take a look at this. It's still in development, but damn, it look promising.
Friday, March 10, 2017
Officer Down
Officer Lucas F. ChellewRest in Peace Bro…We Got The Watch
California Highway Patrol, California
End of Watch: Wednesday, February 22, 2017
Age: 31
Tour: 8 years
Badge # 19402
Officer Lucas Chellew was killed in a motorcycle crash near the intersection of Stockton Boulevard and Fruitridge Road, in Sacramento, while pursuing another motorcycle.
Officer Chellew's motorcycle crashed during the pursuit. The motorcyclist he was pursuing fled the scene and remains at large.
Officer Chellew was a U.S. Army veteran. He had served with the California Highway Patrol for eight years and was assigned to the South Sacramento Area Office. He is survived by his wife, daughter, son, parents and sister. His father was a retired CHP officer and his sister also serves with the agency.
Nemo me impune lacessit
Day is done, Gone the sun, From the lake, From the hills, From the sky. All is well, Safely rest, God is nigh.
Wednesday, March 8, 2017
Officer Down
Police Officer Keith BoyerRest in Peace Bro…We Got The Watch
Whittier Police Department, California
End of Watch: Monday, February 20, 2017
Age: 52
Tour: 27 years
Badge # 247
Police Officer Keith Boyer was shot and killed as he and another officer investigated an accident near the intersection of Colima Road and Mar Vista Street.
Unbeknownst to the officers, the vehicle that caused the crash was stolen and being driven by a gang member who had just been paroled. The parolee had just committed another murder hours earlier. As Officer Boyer attempted to conduct a pat down on the subject, the man suddenly pulled a handgun from his waistband and opened fire. Officer Boyer was killed and a second officer was wounded. Despite the wounds, the officers returned fire and wounded the subject.
Officer Boyer was transported to a local hospital where he succumbed to his wounds.
Officer Boyer had served with the Whittier Police Department for 27 years and was preparing to retire. He is survived by three adult children and his parents.
Nemo me impune lacessit
Day is done, Gone the sun, From the lake, From the hills, From the sky. All is well, Safely rest, God is nigh.
My contribution to the "Day without Women"
Let's just say I'm not exactly impressed with the "Day without Women," more accurately with the "Day without some women working." Personally I've met with several personnel working today and they generally don't have time for this bulls@#$, they have jobs, families to support, etc.
But seeing there are females out there protesting something, here is my contribution. One of Norman Lear's greatest shows, Maude, the cousin of Edith Bunker (if I have to explain this, you're too young for this blog) conducting a bicentennial play, commenting the women of the American Revolution.
As I haven't figured out how to cut the video, I recommend you just go to 20:00. Enjoy!
But seeing there are females out there protesting something, here is my contribution. One of Norman Lear's greatest shows, Maude, the cousin of Edith Bunker (if I have to explain this, you're too young for this blog) conducting a bicentennial play, commenting the women of the American Revolution.
As I haven't figured out how to cut the video, I recommend you just go to 20:00. Enjoy!
Labels:
Comedy,
Society,
Television
Tuesday, March 7, 2017
San Diego Sheriff's K-9s Get Body Armor
A few weeks back a Houston Police K9 was shot by a Houston Police Officer during the pursuit of a robbery suspect. Thankfully Jake is recovering but he may need to take an early medical retirement.
Knowing our K9s are fellow officers and family members, it's good to know more departments are equipping them with body armor.
A little over 500 bucks to protect an animal costing almost ten times as much. Good investment.
| Jake at the emergency room. |
Knowing our K9s are fellow officers and family members, it's good to know more departments are equipping them with body armor.
San Diego Sheriff's K-9s Get Body Armor
The San Diego Sheriff’s Department has a brand new tool for its K-9 unit. All 30 dogs now have bullet-resistant vests.
"It offers an extra level of protection for the dogs to keep them from getting hurt out there in the field," says San Diego County Sheriff’s Department Sgt. Jacob Pavlenko.
"When a handler knows they’re going into a situation where they could be confronting an armed subject, that’s where they’ll put the vest on the dog before they deploy," Pavlenko adds.
Since the vest won’t be on the dog all the time, it takes about 10 to 15 seconds to put on. The vests are lightweight, so the K-9 doesn’t get tired while wearing it. Similar to a bullet-resistant vest for a human, it also protects the dog's body and chest.
"These are ballistic vests, they are to defeat bullets. However, they will defeat slashing moves as well," says Georg Olsen from U.S. Armor.
Money for the vests was provided by the Deputy Sheriff’s Association. The organization paid $16,000 for all 30 of the vests, CW6 reports.
A little over 500 bucks to protect an animal costing almost ten times as much. Good investment.
Labels:
K9
Monday, March 6, 2017
Officer Down
Special Agent Rickey O'DonaldRest in Peace Bro…We Got The Watch
United States Department of Justice - Federal Bureau of Investigation, U.S. Government
End of Watch: Friday, February 17, 2017
Age: 54
Tour: 29 years
Special Agent Rickey O'Donald suffered a fatal heart attack immediately following the FBI's annual mandatory fitness assessment at the Miami Field Office.
After completing the test, he mentioned to other agents that he wasn't feeling well and left. He drove himself to a local hospital where he collapsed in the parking lot.
Special Agent O'Donald had served with the FBI for 29 years and was assigned to the Miami Field Office. He is survived by his wife and daughter.
Nemo me impune lacessit
Day is done, Gone the sun, From the lake, From the hills, From the sky. All is well, Safely rest, God is nigh.
Police, rioters, and social media
One of the points I've made over and over is that cops, like any other human being, have no right to privacy in the public. If I'm on the street,
Good to know Texas is in this group!
And again, what is the problem. You put out a threat to riot in a city, are officers supposed to be blind this warning? If anything, they should be open about this possible riot and be prepared.
A few months ago I was part of the response to a threat in Houston. Originally the rioters (BLM, No My President, etc) were supposed to number around 700. Less than 40 showed up and they were outnumbered more than three to one by the cops (damn near matched by the number of horses.) But according to the American Criminal Lovers Union and this author, the issue is not the threat to the general population by a riot, but the fact police are using public data for being prepared. Thank God these departments are using these assets to know when and where to be deploy. The public expects us to keep them safe from rioters. As Sun Tzu said, thousands of years ago, "Know your enemy and know yourself and you can fight a hundred battles without disaster."
The Switch: Police are spending millions of dollars to monitor the social media of protesters and suspects
Hundreds of local police departments across the United States have collectively spent about $4.75 million on software tools that can monitor the locations of activists at protests or social media hashtags used by suspects, according to new research.
The research, by the Brennan Center for Justice, a nonprofit organization focusing on criminal justice issues, aims to take a comprehensive look at the fast-growing phenomenon of social media-monitoring by law enforcement. Using public records, the Brennan Center tracked spending by 151 local law enforcement agencies that have contracted with start-ups that siphon data from Facebook, Instagram, Twitter and other sites, largely out of the public eye.
“The numbers we have are massively understated,” said Faiza Patel, co-director of the organization’s liberty and national security program, pointing out that agencies don’t always have any obligation to report their use of the software. “But it gives an indication of a phenomenon that is growing rapidly and flying under the radar.”
Top spenders were the City of Los Angeles, the Texas Department of Public Safety, the County of Sacramento, the Florida Department of Law Enforcement and the County of Macomb, which is a large county in Michigan. Each spent roughly $70,000 over the past three years, Brennan found.
Good to know Texas is in this group!
In recent years, a crop of start-ups — with names like Geofeedia, SnapTrends and Dataminr — has sprung up to analyze data posted publicly on popular social media sites. These start-ups buy information from the social sites and analyze the data to look for trends or monitor events taking place at a certain location. Corporations buy the analysis, along with nonprofits, financial firms and, increasingly, law enforcement. The law enforcement trend has exploded in the past two years, Patel said.
Law enforcement officials say the tools can be useful because sometimes people who commit crimes brag about them on social media. Witnesses also may offer up clues, such as posting that they heard gunshots or posting video of events.
But advocates worry that the tools are being increasingly used to monitor protests and other public gatherings, and to target individual activists. The Oregon Department of Justice, for example, used software called Digital Stakeout to monitor people who used more than 30 hashtags on social media including #BlackLivesMatter, according to the American Civil Liberties Union and a lawsuit filed by one of the people who claimed to have been monitored.
Last month, thousands of people used a location-based tool called "Facebook Check-In" at a protest against an oil pipeline at the Standing Rock Sioux Reservation in North Dakota. Many who “checked-in” on Facebook were not physically at Standing Rock but wanted to thwart police who were reportedly monitoring people who were there. Police have denied using such tools at Standing Rock.
Brennan and other advocates say they fear that tracking could increase under President-elect Donald Trump. “Today the main way protesters organize is online,” Patel said. “This is a new administration that has been frankly threatening to the act of political protest.”
Brennan’s data, which tracked local law enforcement and did not examine the much larger spending by federal agencies such as the Federal Bureau of Investigation, was largely obtained from public records requests. The International Association of Police Chiefs has reported that at least 550 law enforcement agencies across 44 states use such tools to gather intelligence.
The rise of social media for law enforcement has become an increasingly perilous issue for technology companies. The companies do not bar law enforcement agencies from buying their data. The companies prohibit its misuse but don’t aggressively track how third parties use it. Last month, Facebook, Instagram and Twitter cut ties with Geofeedia, a software company whose tools have been used by law enforcement to track racially charged protests in Baltimore and in Ferguson, Mo.
And again, what is the problem. You put out a threat to riot in a city, are officers supposed to be blind this warning? If anything, they should be open about this possible riot and be prepared.
A few months ago I was part of the response to a threat in Houston. Originally the rioters (BLM, No My President, etc) were supposed to number around 700. Less than 40 showed up and they were outnumbered more than three to one by the cops (damn near matched by the number of horses.) But according to the American Criminal Lovers Union and this author, the issue is not the threat to the general population by a riot, but the fact police are using public data for being prepared. Thank God these departments are using these assets to know when and where to be deploy. The public expects us to keep them safe from rioters. As Sun Tzu said, thousands of years ago, "Know your enemy and know yourself and you can fight a hundred battles without disaster."
STRATFOR: Ukraine gauges US support, February 22, 2017
Stratfor Senior Eurasia Analyst Eugene Chausovsky examines the uptick in fighting in eastern Ukraine as Kiev measures Washington's support.
We have another R2-FU on the market....
In the days after the Dallas police shooting last summer, where five officers were murdered by a radical anti-cop extremist, the Dallas police used a robot to eliminate this waste of sperm from the human gene pool, I had heated discussions with many people of the use of this technique. Some called it out right murder and I said it wasn't, it was a different version of a sniper. As Dallas PD could not approach the shooter without exposing their officers to fire, the Chief of Police made the call to use this robot. I have no doubt if the sniper had a shot at him, the same call would have made.
Now with some good old American ingenuity, we now have an upgraded version of the R2-FU.
Better and better....
Now with some good old American ingenuity, we now have an upgraded version of the R2-FU.
SHOT Show 2017: Med-Eng Introduces New ‘Avenger’ Robot to Help Bomb Technicians Defeat Terrorist Threats
Med-Eng announced the launch of the Avenger Remotely Operated Vehicle (ROV) at the 2017 SHOT (Shooting, Hunting, Outdoor Trade) Show, Booth #12762. This bomb disposal and tactical robot has been engineered to provide police and military response teams with enhanced capabilities to manage ongoing and emerging threats posed by terrorists, particularly in urban environments where Vehicle-Borne Improvised Explosive Devices (VBIEDS, or ‘car bombs’) are of concern.
The Avenger, designed and manufactured by ICP NewTech, is a mid-sized ROV with most of the operational capabilities typically found only in much larger and more expensive robots. Its performance-to-size ratio is outstanding and reflects the advanced electro-mechanical engineering that guided its development. The Avenger’s highly dextrous arm and claw can easily reach inside, above and below cars, pick-up trucks and delivery vans, to remotely investigate suspicious devices, such as Improvised Explosive Devices (IED).
The system includes an on-board computer that fuses data from multiple Chemical, Biological, Radiological, Nuclear and Explosive (CBRNE) sensors and cameras, and relays it to a command post. This integrated sensor suite provides a mission-critical tool for managing CBRNE and Hazmat threats, such as a terrorist’s ‘dirty bomb’, and mitigating risks to the surrounding public. The numerous sensor ports are compatible with many specialized sensors that bomb squads already have, so they can make use of their existing equipment and attach new tools in the future.
In announcing this new urban response tool, The Safariland Group President Scott O’Brien remarked, “We are very excited to present the men and women on the front lines with a sophisticated robot that will allow them to remotely engage hazardous threats with great effect.” He continued, “The safety of first responders, elite military EOD teams and local citizens is of utmost importance to Safariland and this new system will prove to be an integral part of securing densely populated areas across the United States and the international community.”
Rob Reynolds, general manager of Med-Eng, described the Avenger as, “a robot platform that has real potential to change the landscape of the mid-sized ROV market for the betterment of end users.” He elaborated, “The Avenger combines the mobility and ease of deployment advantages of a mid-sized robot with the reach, lift and sensor-fusion capabilities of bigger platforms. We have been extremely impressed by its performance, technology integration and reliability, and firmly believe it will be readily embraced by bomb squads and EOD teams worldwide looking for a highly effective and affordable robot in a smaller size.”
Eamon Jackson, CEO of ICP NewTech, commented, “We listened very carefully to the needs of end users and recognized the operational challenges they’re facing now and in the foreseeable future. It became clear that response teams needed a robotic platform that could be easily transported through congested urban centers, which meant keeping the robot at a smaller scale. We then applied our engineering expertise to develop a system that could attack a range of VBIED-type threats, overcome obstacles, and give users the freedom to deploy and leverage many of their existing sensors and EOD tools.” He concluded, “The Avenger sets a new high mark that will benefit police and military agencies for years to come....”
Better and better....
Sunday, March 5, 2017
So he "wasn't having an old friend for dinner."
But he did enjoy his petty torments.
Arguable everyone's favorite line from The Silence of the Lambs, Lector's final words to Starling, "I'm having an old friend for dinner," as he hangs the phone up.
In his interview with Barbara Walters just before the Academy Awards in 1992, Barbara had him say it again, at 4:55:
Awesome!
Last week I was looking for a quote from the movie and I accidentally found an earlier version of the screen play. While it is pretty much the same as before, the ending is different. I still prefer the movie one (which is different than the book), but this is great, set up at the beginning of the graduation party. Enjoy!
Arguable everyone's favorite line from The Silence of the Lambs, Lector's final words to Starling, "I'm having an old friend for dinner," as he hangs the phone up.
In his interview with Barbara Walters just before the Academy Awards in 1992, Barbara had him say it again, at 4:55:
Awesome!
Last week I was looking for a quote from the movie and I accidentally found an earlier version of the screen play. While it is pretty much the same as before, the ending is different. I still prefer the movie one (which is different than the book), but this is great, set up at the beginning of the graduation party. Enjoy!
DIRECTOR BURKE (V.O.)
(over loudspeaker)
Congratulations! You are now officers o the Federal Bureau of Investigation...
DISSOLVE TO:
EXT. GROUNDS OF THE FBI ACADEMY - WEEKS LATER - DAY
The forty member of Clarice's class, resplendent in their best dark suits and and dresses, rise, cheering themselves, then turn happily to wave to their audience, as APPLAUSE mounts. Beyond them, on a gaily tented platform, the Director stands behind his podium.
CLARICE AND ARDELIA
look at one another solemnly. Ardelis holds up both fists, in a power shake, and Clarice taps them with her own. She is radiantly beautiful in a navy dress and pearls., the thin scar on her cheek almost healed. Ardelia turns, waving toward the crowd, the Clarice's thoughts are elsewhere. The turns, searching among the dignitaries on the platform, till she locates. \
CRAWFORD
who smiles back at her with quiet pride, and offers a little salute.
CLARICE
grins - more happy than we've ever seen her - then turns to wave towards the crowd with the others.
MOVING ANGLE
over the admiring sea of spectators, several hundred of them, still rising from their folding chairs, APPLAUDING in celebration of these special young people, this perfect, sunlit day. SOUND UPCUT - rock music, laughter - as we...
DISSOLVE TO:
INT. ACADEMY DORM - RED ROOM - THAT NIGHT
A LOUD party is underway - food, beer, dancing -as the new grads celebrate ferociously. Ardelia weaves her way thorough the crowed room, reaches Clarice, who is flanked by her special guest - Pitcher and Roden, the two ardent scientists. Adrelia as to shout at Clarice over the din.
ARDELIA:
Agent Starling! Telephone!
CLARICE
(surprised)
Agent Mapp! Thank you!...
INT. DORM HALLWAY - NIGHT
Clarice picks up the dangling pay phone.
CLARICE
Starling
DR. LECTOR (V.O.)
Well, Clarice, have the lambs stopped screaming…?
She freezes, stunned by the familiar voice. Then she turns, waving frantically toward
ARDELIA
who is just inside the rec room door, at the end of the hall, lost in conversation with Pilchaer and Roden. Ardelia glances at her briefly but misunderstand, waves cheerfully back.
DR. LECTOR (V.O.)
Don’t bother with a trace, I won’t be on long enough.
CLARICE:
turns back, gripping the phone more tightly.
CLARICE
Where are you Dr. Lector
CUT TO:
EXT. A CLEAR NIGHT SKY
Very beautiful, glittering with countless stars.
DR. LECTOR (V.O.)
Where I have a view, Clarice…
MOVING DOWN
we see a rolling lawn, a curving bay. Boars ride at anchor, lights shimmering…
DR. LECTOR (V.O.)
Orion is looking splendid tonight, and Arcturus, the Herdsman, with his flock…
DR. LECTOR
smiles into his mobile phone. He is stretched out on a lounger, on a tiled patio, languidly paring an orange with a penknife. His appearance is quite altered - a beard, glasses, lighter hair. He’s had some cosmetic surgery, as well.
DR. LECTOR
(into phone)
Your lambs are still for now, Clarice, but not forever…You’ll have to earn it again and again, this blessed silence. Because it’s the plight that drives your, and the plight will never end.
CLARICE
Dr. Lector -
DR. LECTOR
I have no plans to call on you, Clarice, the world being more interesting with you in it. Be sure you extend me the same courtesy.
CLARICE (V.O.)
You know I can’t make that promise.
DR. LECTOR
Goodbye, Clarice…
(and then, softly)
You looked - so very lovely today, in your blue suit.
Cut to:
INT. DORM HALLWAY - NIGHT
As Clarice reacts, the full weight of his words sinking in.
CLARICE
Dr. Lector…Dr. Lector…!
But only a dial tone comes from the phone. She is still staring at her received, in shock, as we -
Cut back to:
EXT. THE MOONLIT PATIO
Dr. Lecter sighs, sets his phone down, then rises. Popping an orange section into his mouth, he turns towards the brightly lit house. Stepping delicately over the sprawled body of a uniformed security guard, he walks in through open french doors.
CUT TO:
INT. A BOOKLINE STUDY:
In a swivel chair, amidst the wreckage of his papers and books, is the witching figure of Dr. Frederick Chilton. The extreme intricacy of his bindings recalls Dr. Lecter’s own former restraint. His screams are muffled by the tape over his mouth: he stairs at Dr. Lecter like a rabbit trapped in headlights.
DR. LECTOR
Considers him for a genial moment, then raises the little pen-knife. His eyes are twinkling.
DR. LECTOR
Well, Dr. Chilton. Shall we begin?
FADE OUT
Labels:
Movies
Saturday, March 4, 2017
Officer Down
Major Jay R. Memmelaar, Jr.Rest in Peace Bro…We Got The Watch
Goldsboro Police Department, North Carolina
End of Watch: Thursday, February 16, 2017
Age: 49
Tour: 25 years
Badge # 4502
Cause: Heart attack
Major Jay Memmelaar suffered a fatal heart attack while participating in his department's physical fitness program at approximately 7:00 pm.
He was working out in the department's gym when he began to experience discomfort in his chest. He returned to his office where he collapsed a short time later. He was transported to a local hospital where he passed away.
Major Memmelaar had served with the Goldsboro Police Department for 25 years. He is survived by his wife and two children.
Nemo me impune lacessit
Day is done, Gone the sun, From the lake, From the hills, From the sky. All is well, Safely rest, God is nigh.
Friday, March 3, 2017
K9 Lasso calls it a night....
Good to see it when a fellow officer makes it to retirement. And with almost 500 apprehensions under his belt, Lasso has earned some time off.

Don't knock it Lasso, too many times a cop dies early into retirement. Enjoy yourself, and remember the bitches will love a working stud like you! :<)

Wash. K-9, who helped catch nearly 500 suspects, retires
SPOKANE COUNTY, Wash. — One evening in April 2014, a police dog named Laslo was pursuing a burglary suspect through a mobile home park in Spokane Valley.
The suspect got away, largely because a pit bull chained up nearby broke free and clamped its jaws onto Laslo’s hind leg, leaving a deep gash that required six staples. A veterinarian thought Laslo would need surgery, too.
But the energetic German shepherd recovered faster than expected and a few weeks later, he was back to fighting crime. One night in June 2014, he chased another burglary suspect up a tree at the Avista substation in north Spokane, and tracked down a second suspect from an unrelated crime at a nearby business.
“He’s been a great dog,” said Laslo’s handler, Jeff Thurman of the Spokane County Sheriff’s Office. “He’s really a force multiplier.”
Sunday is Laslo’s last day on the force and Thurman’s last day as a corporal and K-9 handler. Thurman is being promoted to detective and adopting Laslo as a family pet.
The pair have spent four years as law enforcement partners, with Laslo assisting in more than 470 apprehensions.
Deputies say Laslo is unusually talented at sniffing out crime, and that he “contacts” suspects with just the right amount of force. A key player in countless news stories, his name has regularly appeared in The Spokesman-Review and on local TV stations.
“I’ve been around a ton of dogs, but that dog right there, and Thurman, that team is just incredible,” said Deputy Mark Gregory, a Sheriff’s Office spokesman. “It’s a recipe for greatness.”
At 7, Laslo is retiring a year or two younger than most police dogs. He’s still eager to work, but Thurman said he’s been through enough.
In July 2013, Laslo was sent to apprehend an assault suspect hiding in a camper in Liberty Lake. The man struck Laslo in the face with his arm, which was wrapped in a hard cast, several times until the dog’s nose bled.
Several months later, Laslo was attacked again during a SWAT raid on the South Hill. And in January 2016, Laslo and Thurman encountered two more pit bulls in Spokane Valley. Laslo, who was wearing a ballistic vest, was uninjured after one dog tried to bite his neck, while Thurman received a puncture wound on his leg...
...Thurman said the dogs are indispensable partners in the effort to keep Spokane County safe.
In many cases where a suspect runs away, “had it not been for the K-9, we might never have known who they were,” Thurman said. “It’s a lot safer for the community, a lot safer for the deputies out here searching.”
Thurman, a 21-year law enforcement veteran, will be one of the first detectives on Spokane Valley’s new Burglary Task Force. The job will be a little easier, he said, with Laslo waiting for him at home.
“He’s a real social dog,” Thurman said. “He knows the difference between work and home life.”
Don't knock it Lasso, too many times a cop dies early into retirement. Enjoy yourself, and remember the bitches will love a working stud like you! :<)
Labels:
K9
An alternative look at China/North Korea
Last week I posted a STRATFOR article on China moving to "put North Korea in its place." The regular readers and my friends know I've been intersted in North Korea for decades and their ability to survive in spite of incredible isolation. Also, if ever there was a 1984 nation on earth, this is it. I remember reading an interview with Europeans who visited the nation and the population is unaware that man arrived on the moon. One doctor who spent a year there determined the average North Korean was three inches shorter than the average South Korean because of malnutrition.
Now this is interesting. I remember writing a paper on North Korean cyber-warfare and how their facilities are housed in China. China is very interested in keeping the West, particular the United States, off balance and NK cyber attacks help in that effort. And obviously China will allow North Korea to keep operating in China, as long as they serve a purpose.
From Foreign Policy, an interesting article:
Interesting read all in all. Open source I've read is that the Chinese leadership told the South Korean government, indirectly, that when North Korea collapses they will huff and puff, but they will not invade again if the Americans stay on the south side of the peninsula. We'll see how that works out as North Korea is dying. And it will be a great day when the Kims are hanged from the capital in Pyongyang.
Now this is interesting. I remember writing a paper on North Korean cyber-warfare and how their facilities are housed in China. China is very interested in keeping the West, particular the United States, off balance and NK cyber attacks help in that effort. And obviously China will allow North Korea to keep operating in China, as long as they serve a purpose.
From Foreign Policy, an interesting article:
Confidential U.N. Report Details North Korea’s Front Companies in China
A maze of shadowy businesses allows Kim Jong-un to evade sanctions and experts say there's no way Beijing doesn't know.
When China announced last week plans to cut off imports of coal from North Korea, a vital source of revenue for the cash-starved Hermit Kingdom, it fueled optimism that Beijing may be getting serious about reining in its erratic neighbor.
But an unpublished U.N. report obtained by Foreign Policy that documents sophisticated North Korean efforts to evade sanctions shows that China has proved a fickle partner at best in Washington’s effort to stymie Pyongyang’s nuclear ambitions...
...North Korea “is flouting sanctions through trade in prohibited goods, with evasion techniques that are increasing in scale, scope and sophistication,” according to the report compiled by an eight-member panel, which is chaired by a British national and includes experts from China, Russia, and the United States. The North Korean schemes are “combining to significantly negate the impact” of international sanctions.
China, despite its apparent cooperation of late with international efforts to sanction North Korea, has instead served as Pyongyang’s economic lifeline, purchasing the vast majority of its coal, gold, and iron ore and serving as the primary hub for illicit trade that undermines a raft of U.N. sanctions that China nominally supports, the report’s findings suggest.
As early as December 2016, China had blown past a U.N.-imposed ceiling of 1 million metric tons on coal imports, purchasing twice that amount. China then shrugged off a requirement to report its North Korean coal imports to the U.N. Security Council sanctions committee. When U.S. and Japanese diplomats pressed their Chinese counterpart for an explanation in a closed-door meeting this month, the Chinese diplomat said nothing, according to a U.N.-based official.
North Korean banks and firms, meanwhile, have maintained access to international financial markets through a vast network of Chinese-based front companies, enabling Pyongyang to evade sanctions. That includes trades in cash and gold bullion and concealing financial transactions behind a network of foreign countries and individuals, allowing North Korea to gain ready access to the international financial system, as well as to banks in China and New York. North Korea’s business “networks are adapting by using greater ingenuity in accessing formal banking channels as well as bulk cash and gold transfers,” the report found.
There is no direct evidence that the Chinese government is actively supporting North Korea’s sanctions busters.
But William Newcomb, a former member of the U.N. sanctions panel on North Korea, said it is hard to believe China is unaware of the illicit trade.
“You have designated entities that have continued to operate in China,” he told FP. “It’s not an accident. China’s security services are good enough to know who is doing what” inside their country...
Interesting read all in all. Open source I've read is that the Chinese leadership told the South Korean government, indirectly, that when North Korea collapses they will huff and puff, but they will not invade again if the Americans stay on the south side of the peninsula. We'll see how that works out as North Korea is dying. And it will be a great day when the Kims are hanged from the capital in Pyongyang.
Thursday, March 2, 2017
Talk about good training on getting over an obstacle...
I'm not SWAT, and I'm not one to go up like this. But this is some great training.
Subscribe to:
Posts (Atom)